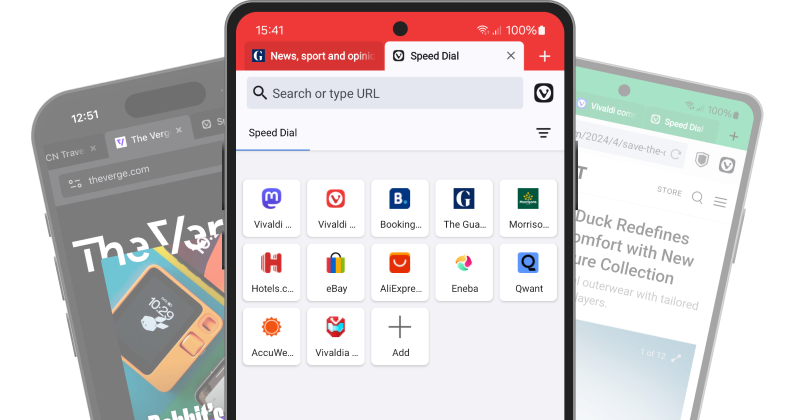
Come together on Vivaldi Social
Follow anyone across the Fediverse and say goodbye to algorithms and intrusive ads.
Experience real social media freedom with Vivaldi Social, our independent server on Mastodon.
Visit Vivaldi Social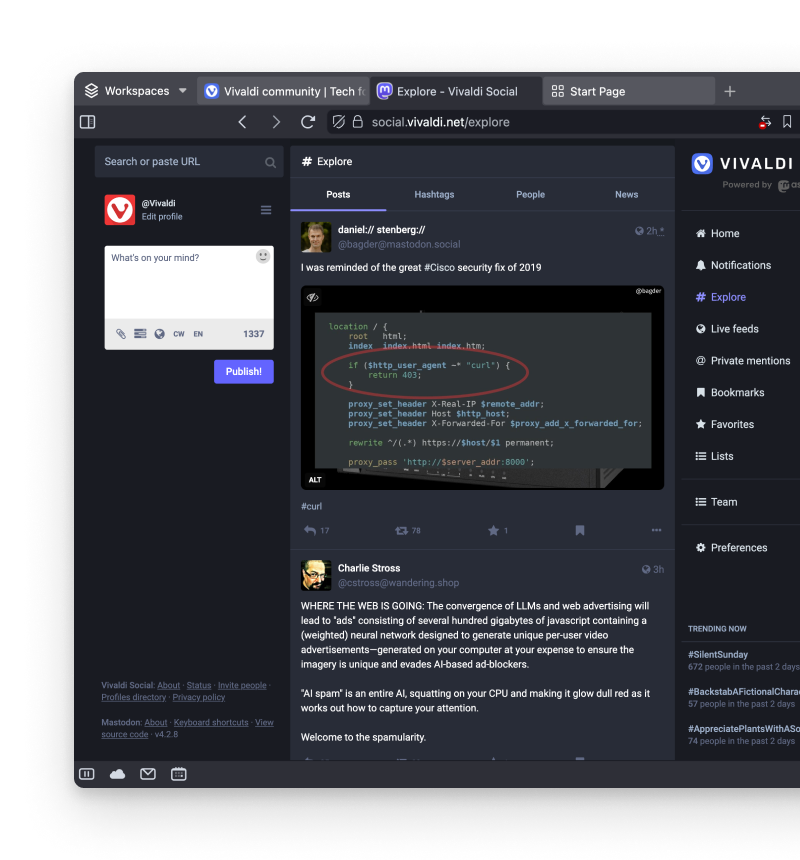
Community Talks
Listen to other community members as they discuss their favourite features of Vivaldi, why being on the Fediverse is important, or how regulation can help create a fairer browser space.
No talk this month, but we’ll be back in August!
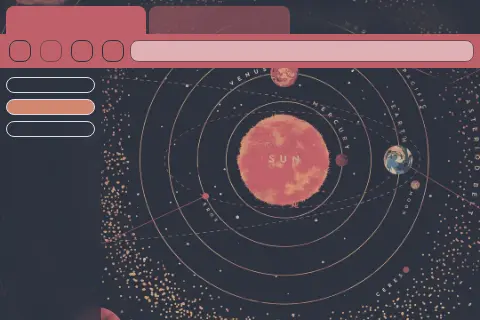
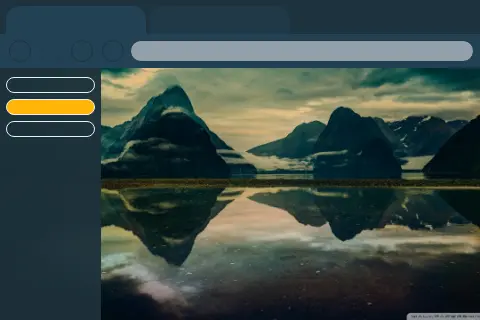
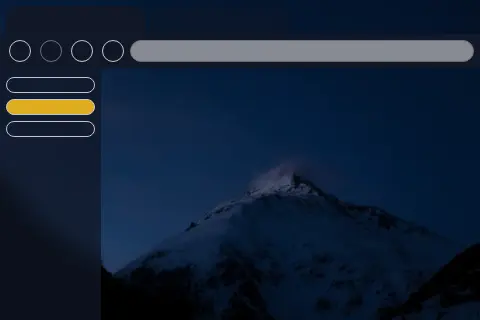
Themes
Give your Vivaldi browser a fresh look. Pick from hundreds of themes or create your own to share with the Community.